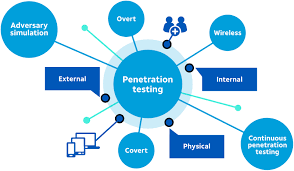
Three Types of Penetration Testing
There are three main types of penetration testing: white-box, black-box, and black-box reconnaissance. White-box involves obtaining access to network and application components, whereas black-box focuses on reconnaissance. White-box penetration tests involve obtaining access to applications and networks, as well as exploiting a known vulnerability in those components. While black-box attacks focus on unauthorized access, white-box penetration tests also examine a human network.
types of penetration testing
White-box testing is the most comprehensive of all three, and is the most common form of penetration testing. Unlike the black-box approach, white-box penetration testing gives testers full access to target systems and simulates an attack by an internal source. It examines code coverage, data flow, and path testing to identify vulnerabilities that can be exploited by an attacker. This method also performs syntax and typographical checks.
Social-Engineering-based penetration testing assesses the vulnerability of employees to hacking and stealing sensitive data. These attacks often involve tricks to convince employees to share private information or perform actions that expose that information. Phishing emails are a prime example. Hackers may pose as a manager and ask an employee for a login or transfer money. White-hat penetration tests use social-engineering tactics to exploit employees and reveal the need for greater employee security training.
What Are the Three Types of Penetration Testing?
White-box pen testing is another type of penetration testing that focuses on vulnerabilities that are hidden in the code. This type of testing involves exploiting various application and web-app endpoints, which requires considerable time and planning. Black-box pen tests, however, are less specific, as they only capture low-hanging problems in the software code. Grey-box pen tests also tend to be more sophisticated and targeted.
White-box penetration tests require a thorough knowledge of the target system. Because the attackers do not have time constraints, they can focus on internal vulnerabilities. However, real-life attackers do not have the luxury of time and may work on an attack plan for months before executing the attack. Moreover, defensive tools have come in to the scene to protect against vulnerability exploits. Some web browsers have built-in settings that block the exploit. This means that attackers will require different settings to exploit a vulnerability.
White-box penetration tests use techniques aimed at exposing weak physical security barriers. White-box penetration testing requires that the tester is aware of the environment before conducting the test. Uncertified OSS (open source software) is also an example of homegrown threats. It can be used to extend or create homemade applications that present severe unanticipated threats. White-box penetration testing also helps businesses and organizations to implement better cybersecurity policies and strategies.